XRPL NFT Scam Tracker
The XRP-API.com NFT phishing-drain campaign tricks Xaman and other wallet users into signing "Safe XRPL verify message" transactions that drain their funds. This page tracks every confirmed drain on-chain and auto-updates as new scams are detected.
Campaign first observed 2026-01-25 · latest drain 2026-05-17 · data refreshed 0s ago
Ecosystem warning
David "JoelKatz" Schwartz, CTO of Ripple, has publicly warned XRPL users about this campaign. View on X →
Victim testimony
@xZBLUEx, FuzzyBear community member, was drained after accepting a bait NFT offer that swept his FUZZY holdings. View on X →
Fully understand any transaction before you sign it. Transactions on the XRP Ledger are final and cannot be reversed.
How victims are lured in
The hook. The attacker first social-engineers the victim with a fake airdrop, reward, staking, or token-claim opportunity, usually framed with urgency ("limited slots", "ends in 1 hour", "verify in the next 10 minutes"). The lure links to a phishing page that prompts you to connect your wallet. Connecting alone does not drain anything: the wallet just shares its address so the attacker can scan your balances. The drain only happens once you sign a transaction the attacker pushes to your wallet.
The same operator group runs multiple acquisition funnels in parallel:
- X / Twitter spam. Dozens of fake accounts posing as Xaman support, Xaman developers, or admins of trending projects. Profiles are padded with purchased followers and bot engagement (likes, replies, retweets) to look legitimate at a glance. They reply to real users in trending XRPL threads with "verification" instructions linking to the bait.
- Targeted impersonation. The dominant lure is Xaman("your wallet needs verification"). Variants impersonate community-favorite projects like PHNIX, FuzzyBear, and other meme or DeFi tokens currently in the spotlight. The same drain mechanic adapts to whichever brand the victim trusts.
- Telegram & Discord DMs. After a user posts a support question or joins a project channel, attackers DM them within minutes claiming to be a "support agent" or "moderator". They funnel the conversation off the official server and into a one-on-one DM where they push the verification link or terminal-paste command.
- Google search hijacking. The campaign runs typo-squatted domains and pays for Google Ads slots that appear above the real result when users search for XRPL wallets, marketplaces, or token names. A single character difference in the URL bar (or just clicking the top "Sponsored" result) lands them on a clone site that runs the same scripts.
Common thread: the attacker's only goal is to get the victim onto a page they control, or to get them to sign a transaction or paste a terminal command without reading it. The on-chain drain or the malware payload then follows automatically.
Attack flow at a glance
End-to-end path from first contact to drained wallet:
Fake airdrop or reward on X, Discord, Telegram, or a Google-Ads phishing site.
Victim connects Xaman / Crossmark / GemWallet. Address shared, no funds moved yet.
Attacker pushes NFTokenCreateOffer prompts non-stop, disguised as 'verification'.
How the scam works (on-chain drain)
The attacker pre-targets the victim. After scanning their wallet, the attacker mints one NFT per asset the victim holds: XRP, LP tokens, IOUs, everything. Each NFT's URI encodes that specific balance, e.g. https://xrpl-api.com/api/nft/metadata?amount=11432359&asset=CSC%3ArCSCManTZ8ME…. The phishing endpoint dynamically returns matching metadata so each NFT renders in the victim's wallet as a stand-in for that exact balance, often dressed up to impersonate Xaman, XRPL.org, or a known marketplace.
The attacker then creates NFTokenCreateOffers with memos like "Verification: Safe XRPL verify message" plus "Info: idx:0;len:11". The wallet UI shows what looks like a routine verification, but each signature actually authorizes a sale of the targeted balance. Signing N "verifications" hands the attacker N specific assets: XRP first, then every held token.
When the victim signs, the attacker accepts the offer. The transfer is a normal on-chain payment, indistinguishable from a legitimate trade. There is no path to reverse it.
Evolving evasion. As detection has tightened across XRPL platforms and wallets, the campaign has shifted. The most recent variants mint blankNFTs with minimal or no on-chain metadata (no URI, no memo, sometimes no name), so URI and memo classifiers have nothing to match. We catch these by issuer-level reputation: any wallet that has ever produced a confirmed scam is auto-flagged on every subsequent mint and offer, URI or not. The list refreshes live and is published as scamIssuersList in the /api/nft/scam response so wallets can mirror it client-side.
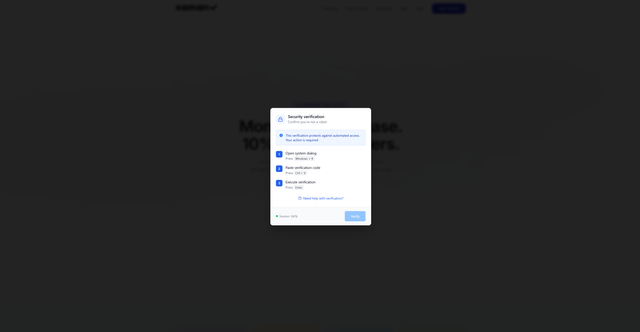
Off-chain variant: terminal stealer payload
The same operators run a parallel attack that never touches the ledger. The bait NFT or a linked page prompts the user to "complete verification" by copying a string and pasting it into their desktop terminal (PowerShell on Windows, Terminal on macOS). The pasted line fetches a payload from a short-lived host (e.g. mmzzxcca.xyz/update3.zip) which deploys HijackLoaderplus SnappyClient, a commodity-stealer combo that exfiltrates browser cookies, saved passwords, and cryptocurrency wallet files, and installs persistence via a Run key plus DLL injection into SysWOW64\input.dll. See the public sandbox detonation at tria.ge/260505-k76d4afx2j (severity 10/10).
There is no XRPL signature involved: the loss happens entirely on the victim's machine, and the attacker can sweep funds from any wallet whose seed or session cookie was stored locally. Never paste anything from an NFT, Discord, Twitter, or website prompt into a terminal. No legitimate XRPL service ever asks you to do this.
Monthly drain timeline
| Month | XRP drained | Drain events |
|---|---|---|
| 2026-05 | 725.6K | 175 |
| 2026-04 | 231.5K | 135 |
| 2026-03 | 102.3K | 49 |
| 2026-02 | 434.8K | 151 |
| 2026-01 | 9.8K | 44 |
Top scammer wallets (XRP received)
| Address | XRP | Drains |
|---|---|---|
| r3qAzD…x6ia | 577.1K | 10 |
| rKWQGG…MaTp | 352.0K | 103 |
| rG8Vfi…1UTq | 192.4K | 105 |
| rNRvAX…ev4k | 76.1K | 25 |
| rfAJ3d…KHD2 | 47.1K | 23 |
| rpQ2gH…fQv1 | 39.7K | 19 |
| rGtC5i…Z22M | 34.5K | 13 |
| rJtuQr…2yZj | 34.4K | 13 |
| r3KmVn…B8Xr | 23.1K | 6 |
| rKzhn5…PDzf | 21.6K | 5 |
Top victim wallets (XRP paid)
| Address | XRP | Drains |
|---|---|---|
| rGhwR5…X2xG | 556.1K | 1 |
| rn6jfs…RvFB | 259.5K | 3 |
| rnw9bP…T8ZT | 79.0K | 1 |
| rnx9XF…8Lob | 56.8K | 1 |
| rwDjHF…LcJC | 40.4K | 1 |
| rh1avy…ZVGW | 39.7K | 1 |
| rL8RPD…gsTs | 33.2K | 4 |
| rGVW8W…bBgc | 31.6K | 1 |
| r3miTG…H92u | 30.0K | 1 |
| rnrLUb…87R3 | 23.5K | 2 |
Scammer wallet holdings (live)
Current on-chain holdings of every scam wallet, XRP plus IOU/LP tokens at market value. Compare against the 1.50M XRP-equiv drained from victims: 96% has already been moved off-chain (cashed out, bridged, or pushed through a tumbler).
| Wallet | Total (XRP-equiv) | XRP cash | Tokens |
|---|---|---|---|
| rKWQGG…MaTp 19.97M Smugler63 CRTX6.17M REITF7.1K ARUNA | 45.0K | 41 | 45.0K |
| rak87m…EfLz 5.0K DBK0 BITx | 10.0K | 5 | 10.0K |
| ra5iV5…gyfx 9.4K ASC2.4K RPR | 2.0K | 2.0K | 14 |
| rMWj9F…RHAJ | 743 | 743 | 0 |
| r37JxY…V5j9 13.0K xSPECTAR124.7K XVR373.6K TXT138 CSC | 595 | 520 | 75 |
| rPMHza…7DNy 3.76M propx54 xDREAMS15.38M XGBL57 SOLO | 481 | 16 | 465 |
| rfAJ3d…KHD2 9.15M FUZZY6.6K XRPH1.59M PHNIX7 RLUSD | 452 | 9 | 443 |
| r4W4fi…8vu4 11.52M FUZZY178 VGB2.7K ELS52 XPM | 422 | 6 | 416 |
| rsXHyu…6ruc 23.64M PHNIX14.8K XFT | 330 | 3 | 327 |
| r3qAzD…x6ia 16.8K XPM0 MAG90.5K FUZZY63 SOLO | 182 | 6 | 176 |
| rnsMwz…NcTD 11.11M ATM1.04M FUZZY0 MAG23.5K ALBA | 128 | 7 | 121 |
| rG8Vfi…1UTq 2.4K FLR690 XAH1.1K CTF7.9K PLR | 125 | 53 | 72 |
| rMZGH5…JAtc 7 DROP892.5K XMEME118 XRPH6.37M SEAL | 82 | 55 | 27 |
| rGtC5i…Z22M 35 RLUSD200 +9.579977 XRP10.0K LP XRP9/XRP728 LP Recieving: + 3 XRP/XRP | 80 | 20 | 60 |
| rphrC8…MLP8 13.6K BEAR18.2K ARK1.39M MALLARD463.7K editions | 70 | 17 | 53 |
| r38ypQ…tSNy 13.0K BEAR1.2K SOLO178.8K MXI306 XRT | 67 | 7 | 60 |
| ra4wm3…ta7Y 88 Equilibrium | 64 | 64 | 0 |
| rpQ2gH…fQv1 3.41M PHNIX169 SOLO0 LOL0 REAL | 58 | 8 | 50 |
| rDWBsv…VWsV 999 SOLO1.07M PHNIX1.1K VGB5 RLUSD | 55 | 9 | 47 |
| r3ma7d…sPHQ 2.9K REAL228.3K PHNIX1.3K BEAR354 BXE | 27 | 6 | 20 |
Snapshot from the last cron run (37s ago). Top 20 wallets shown. Chips list each wallet's top tokens (purple = LP); hover for full value.
Potential dump pressure: tokens held by scammers
Aggregate token positions across all 138 scam wallets. If any of these tokens see a large market sell, the scammers are likely behind it. Sorted by current XRP-equivalent.
| Token | Issuer | Amount held | Value (XRP) | Wallets |
|---|---|---|---|---|
| Smugler | rNZYZo…zyR6 | 19.97M | 40.4K | 1 |
| DBK | r3coGG…JMEd | 5.0K | 10.0K | 1 |
| CRTX | rfVhtw…tgT6 | 63 | 3.1K | 1 |
| REITF | rLSCBS…LygX | 6.17M | 792 | 1 |
| FUZZY | rhCAT4…pR62 | 21.93M | 788 | 52 |
| ARUNA | rfjqDH…LzKm | 7.1K | 590 | 1 |
| PHNIX | rDFXbW…ivmN | 30.02M | 414 | 38 |
| propx | rDXPvU…Lnb4 | 3.76M | 364 | 1 |
| MAG | rXmagw…vVMJ | 0 | 114 | 8 |
| xDREAMS | raJt8a…EAit | 54 | 96 | 1 |
Top 10 by current XRP-equivalent. 40 distinct tokens total.
Tokens drained (top 40 by frequency)
Value in XRP uses current market price for regular tokens, or AMM pool reserves for LP tokens. - means no price feed (illiquid or delisted).
| FUZZY | rhCAT4…pR62 | 593.42M | 21.3K | 25 |
| PHNIX | rDFXbW…ivmN | 2.06B | 28.1K | 18 |
| SOLO | rsoLo2…rLZz | 51.2K | 775 | 17 |
| RLUSD | rMxCKb…m5De | 1.2K | 829 | 15 |
| REAL | rKVyXn…Nz88 | 36.9K | 132 | 9 |
| BXE | rM1J2M…y87r | 116.1K | 699 | 7 |
| 03C3BE9D…LP XRP/MAG | rNZ2ZV…bXce | 181.5K | 8.8K | 7 |
| XPM | rXPMxB…wkoa | 18.5K | 95 | 7 |
| VGB | rhcyBr…knaU | 17.2K | 93 | 7 |
| CSC | rCSCMa…gkwr | 377.96M | 13.2K | 7 |
Recent drains (live feed)
Each row links to the on-chain transaction and the bait NFT. Hover any abbreviated value to see the full ID.
| When | Victim | Scammer | Paid | Bait NFT | Tx |
|---|---|---|---|---|---|
| 5h ago | rKxHtS…rfvZ | ra5iV5…gyfx | 6.3K XRP | 00090000…48CF | A6E71E8C…BF49 |
| 6h ago | rfPZdd…Jgue | ra5iV5…gyfx | 198 XRP | 00090000…48B6 | B4404F9C…513F |
| 7h ago | rB9PPr…BNy1 | ra5iV5…gyfx | 80.4K LP XRP/RPR≈ 14 XRP | 00090000…48B0 | 9FF85201…DC6B |
| 7h ago | rB9PPr…BNy1 | ra5iV5…gyfx | 163.9K LP XRP/ASC≈ 15 XRP | 00090000…48AF | CABD3518…D2CE |
| 19h ago | rnDLNN…WV7q | raMAki…4bjh | 94.4K BEAR≈ 203 XRP | 00090000…9DAF | 40C7D61B…9B01 |
| 19h ago | rnDLNN…WV7q | raMAki…4bjh | 300 RLUSD≈ 212 XRP | 00090000…9DAE | 34BD276D…4866 |
| 19h ago | rnDLNN…WV7q | raMAki…4bjh | 13.11M FUZZY≈ 471 XRP | 00090000…9D86 | 7BF20CA3…A2A5 |
| 21h ago | rKPXP4…N9ij | raMAki…4bjh | 52 XRP | 00090000…9DA6 | F25AA019…2F92 |
| 23h ago | rHPEKk…4UAt | raMAki…4bjh | 7 XRP | 00090000…9DA4 | DF7BFE06…8795 |
| 24h ago | rw29uH…Gm7a | raMAki…4bjh | 5.5K XRP | 00090000…9DA3 | C4E8D1D9…7212 |
Drains ≥ 10,000 XRP highlighted in red. Scammer wallets in red, victims in blue.
How to protect yourself (users)
- Never sign an
NFTokenCreateOfferfor an NFT you didn't deliberately list. - Treat memos like "Verification", "Safe XRPL verify", or "idx:N;len:N" as red flags. No legitimate XRPL service uses those.
- If an NFT in your wallet shows a huge balance you never bought, do not click it. Check the URI: anything pointing to
xrpl-api.comorxrp-api.comis the drain campaign. - Burn or hide suspect NFTs from your wallet instead of interacting with them.
- Never paste a "verification" code into your terminal. If an NFT description, linked page, Discord/Twitter DM, or "support agent" tells you to open PowerShell/Terminal and paste a command, it is HijackLoader/SnappyClient or an equivalent commodity stealer. It will exfiltrate your browser cookies, saved passwords, wallet files, and stage persistence on your machine. No real XRPL service ever requires this.
- If you've been drained on-chain, the transfer cannot be reversed. If your machine was compromised (terminal-paste variant), assume cookies + saved credentials + locally stored wallet seeds are all leaked: rotate exchange/email/social passwords from a clean device, revoke any active wallet sessions, and move XRPL funds to a fresh seed generated offline on hardware you trust.
Already got the spam offers? Revoke Xaman third-party app access
If you connected your Xaman wallet to one of the phishing sites and are now being spammed with NFT offers, cancelling each offer does not stop the attack. The attacker holds an active third-party app permission on your wallet and will keep pushing offers until you revoke it.
- Open Xaman → Settings → Third-party apps.
- Look for an app you don't recognise. Most commonly the malicious entry is labelled "XPMarket", but the attacker can rename it to anything (Xaman, FuzzyBear, RLUSD, an XRPL marketplace, etc.). The displayed name is not verified.
- Tap the suspicious app.
- Scroll to the bottom and tap Revoke access.
After revoking, the attacker can no longer create offers on your behalf. If you signed anything during the session, or if you can't remember exactly what you authorized, move remaining XRP, tokens, and any LP positions to a fresh seed generated offline.
For wallet & dapp developers: automatic scam detection
Two free public endpoints cover the full integration surface. No API key required; data updates every minute.
GET /api/nft/<NFTokenID>Already part of the standard NFT API. Returns the full NFT document; check the scam: true and scamType fields before rendering or accepting an offer.
curl https://api.xrpl.to/api/nft/00090000560ABF36DE406A9E7EE3B37CBBE047629EC1C40E956828E50634B54A
# → { "_id": "0009...", "scam": true, "scamType": "phishing_uri_domain", "issuer": "r3qAz...", ... }GET /api/nft/scamSingle endpoint with everything: aggregate stats, monthly timeline, top scammers/victims, recent drains, and a flat scamIssuersList (139 addresses today) for client-side filtering. Cache locally and filter incoming NFTs by issuer against the list; pre-empts any per-NFT round-trip for known-bad wallets. Refresh every few minutes.
curl https://api.xrpl.to/api/nft/scam
# → { "totals": { ... }, "monthlyTimeline": [ ... ], "topScammers": [ ... ],
# "tokensDrained": [ ... ], "recentDrains": [ ... ],
# "scamIssuersList": ["r3qAz...", "rGhwR5...", ...], ... }Suggested integration: on app load, fetch /api/nft/scam once and cache the scamIssuersList. For each NFT before rendering, check nft.issuer ∈ scamIssuersList first (O(1) client-side). If the issuer is clean but you want to verify the specific NFT, follow up with GET /api/nft/<NFTokenID>and check scam in the response. Detection is already live; flags appear on-chain within seconds of a new mint or offer.
The full XRPL.to API surface (tokens, AMM pools, NFTs, traders, OHLC, holders, search, and more) is documented at xrpl.to/docs. Free, no API key required for read endpoints, no rate-limit headaches for normal use. Drop-in replacement for the deprecated Ripple Data API.